You may have scratched your head at the title of this post. What is phishing and what in the world does whaling have to do with your law practice? Phishing is a cyber attack technique that has been around for quite a few years. With the constant evolution of cyber threats, what was once phishing has now expanded into an even bigger risk, known as whaling.
What is Phishing?
Phishing is the fraudulent use of emails, telephone calls and false websites to gather valuable information and financial data. It works by installing a software into your computer, which gathers information and sends it back to the cyber hacker. We’ve all heard of phishing attacks at one time or another. It usually comes as a warning not to open a particular email or attachment.
According to the Microsoft security website, there are particular clues that may alert you to a phishing email, including:
- Poor grammar and misspelled words. Real companies spend the time and money to edit and proofread their email correspondence. You are not going to get a legitimate email from the Facebook with the word “social” misspelled.
- Links within the email that do not match the actual web address. Without clicking on the link, place your mouse over it and hover. The actual web address will show up underneath the link. If the two don’t match, you have probably received a phishing email message.
- Threats or warnings about compromised security. These emails often contain threats that your system’s security will be compromised if you do not take action or they may state that your system has already been hacked and further action is required. Don’t fall for these tricks.
- Claimed connection to a legitimate company or organization. In an attempt to look legitimate and gain your trust, these hackers often pose as legitimate companies, using their names and images. If something does not look quite right, it’s probably wrong.
Comparitech also has a good blog on how to recognize and avoid common phishing tactics.
What is Whaling?
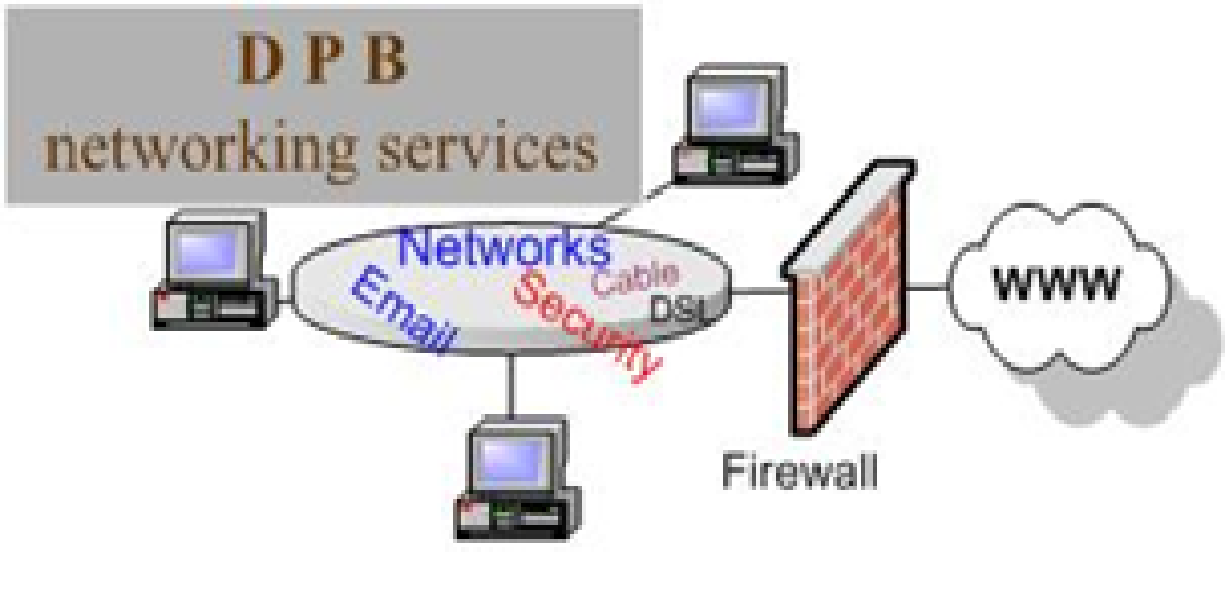
Whaling takes phishing to the next level, by specifically targeting top level executives and managers. It is a much more targeted attack, aimed at obtaining sensitive information from corporations and successful businesses. While whaling attempts resemble phishing tactics, they up the stakes by asking for specific banking information or an immediate payment. A whaling message may also appear more official, sometimes even appearing to come from someone within your organization. For example, a manager directing an administrator to make payment on an account. Whaling hackers also commonly use law enforcement agencies, like the FBI, in their email messages.
Protecting your Firm
When implementing cyber security tactics, you are not only working to protect your firm. You are also working to protect the confidential data of your clients. It only takes one successful phishing or whaling attempt to put client’s information into the hands of hacker. Some of the steps you should take include:
- Regularly scheduled software updates
- Security audits
- Employee training
- Installation of protection solutions
The folks at TimeSolv understand the sensitivity of your firm and client information. That’s why they use the latest security standards and techniques to safeguard your data. TimeSolv is hosted by a state-of-the-art data center provided by Amazon Web Services (AWS) and highly encrypted 256-bit SSL is used for data transmission between your browser and our data center. To learn more about TimeSolv’s security and reliability, click here for a no-obligation free trial offer.
About Erika Winston:
Erika Winston is a freelance writer with a passion for law. Through her business, The Legal Writing Studio, she helps legal professionals deliver effective written messages. Erika is a regular contributor to TimeSolv and a variety of other publications.